MCP-040
Advanced 4-Door Access Control & Security Controller
MCP-040 is a high-performance multi-door access control controller designed for enterprise-grade security systems. It supports up to four doors and integrates seamlessly with biometric readers, RFID devices, and third-party systems, ensuring centralized and intelligent security management.
In addition, it is engineered for large-scale installations where reliability and scalability are critical. Therefore, MCP-040 combines access control, intrusion detection, alarm management, and real-time monitoring into one unified platform suitable for demanding environments.

MCP-040 Access Controller Overview
MCP-040 Access Controller is a powerful solution for managing multi-door security systems efficiently. Moreover, it provides stable performance for enterprise environments that require strict access control policies.
MCP-040 Access Controller Key Features
The MCP-040 Access Controller delivers advanced security capabilities, and it is designed to handle complex access environments with ease.
- Controls up to 4 Doors (4 Lock Outputs)
- Supports up to 8 Readers (Fingerprint / Face / RFID / Wiegand)
- Integrated 8-Zone Intrusion Alarm System
- TCP/IP Network Communication
- RS-485 Secure Communication Protocol
- Wiegand Input/Output Support
- 8 Programmable Outputs
- 8 Zone Monitoring Inputs
- Built-in Alarm & Siren Control
- Standalone or Server-Based Operation
- Anti-Passback & Interlock Functions
- Large Event Log Storage

MCP-040 Power & Backup System
Additionally, the controller supports an external backup battery, which ensures continuous operation during power failure scenarios. As a result, security systems remain active without interruption.
Backup battery is available in case of a power outage, which improves system reliability in critical environments.
Intelligent Multi-Door Control System
MCP-040 is designed to manage complex access environments efficiently. Users can define multiple security levels across doors and zones, which enhances operational flexibility.
Furthermore, the system operates in both online and offline modes. Consequently, it continues working even if the network connection is temporarily lost.
MCP-040 Access Controller Intrusion Detection
One of the key advantages of MCP-040 Access Controller is its integrated 8-zone intrusion detection system. Each zone can be connected to multiple security sensors.
- Door Contact Sensors
- Motion Detectors (PIR)
- Panic Buttons
- Smoke Detectors
- Alarm Devices
As a result, real-time monitoring becomes possible, and security teams can respond immediately to any unauthorized activity.
MCP-040 Access Controller Flexibility
MCP-040 Access Controller supports multiple authentication devices, making it highly flexible for different security setups.
- Fingerprint Readers
- Face Recognition Terminals
- RFID Card Readers
- PIN Keypads
In addition, it supports up to 50,000 users and stores more than 51,200 event logs, making it suitable for enterprise-scale deployments.
Enterprise Applications
MCP-040 Access Controller is widely used in critical infrastructure and high-security environments such as:
- Corporate Headquarters
- Industrial Facilities
- Government Buildings
- Hospitals
- Banks & Financial Institutions
- Educational Campuses
- Data Centers
- High-Security Sites
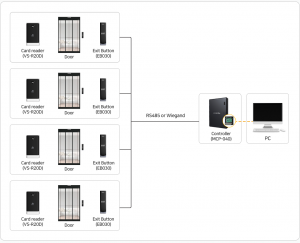
MCP-040 System Architecture
The MCP-040 Access Controller acts as the central brain of a multi-door security system. It connects readers, locks, sensors, and alarms into a unified network.
Moreover, it supports real-time validation, centralized server monitoring, distributed control, and multi-zone security partitioning.
Why Choose MCP-040 Access Controller?
MCP-040 Access Controller is not just a hardware unit; it is a complete security management platform. Unlike basic controllers, it integrates access control, intrusion detection, and multi-door management in one system.
Therefore, it is ideal for organizations that require maximum control, scalability, and long-term reliability in their security infrastructure.